In 2026, the digital landscape is more interconnected and, unfortunately, more hostile than ever. Cyber threats aren’t just an inconvenience; they’re a constant, evolving challenge for businesses and individuals alike. From sophisticated phishing campaigns that trick even the most vigilant users to stealthy malware establishing command-and-control (C2) channels, the attack surface keeps expanding. Traditional perimeter defenses, while still vital, often fall short against the sheer volume and ingenuity of modern attacks. This is where a DNS Firewall steps in, offering a remarkably effective and often underestimated layer of defense.
Understanding the Foundation: What is DNS and Why Does It Matter So Much?

Before we dive into how a DNS Firewall works, let’s briefly revisit the Domain Name System (DNS) itself. Think of DNS as the internet’s phonebook. When you type a website address like “example.com” into your browser, your computer doesn’t instantly know how to reach it. Instead, it sends a DNS query to a DNS resolver (often provided by your ISP or a public service like Google DNS). This resolver then translates “example.com” into an IP address, like 192.0.2.1, which is the actual numerical address computers use to find each other on the network. Every single interaction you have online, from browsing a webpage to sending an email or using a cloud application, typically begins with a DNS query. This makes DNS a fundamental, invisible part of virtually all internet activity. Because it’s so fundamental and often overlooked as a security control point, it has become a prime target and vector for cybercriminals.
How a DNS Firewall Works: Intercept, Inspect, Block
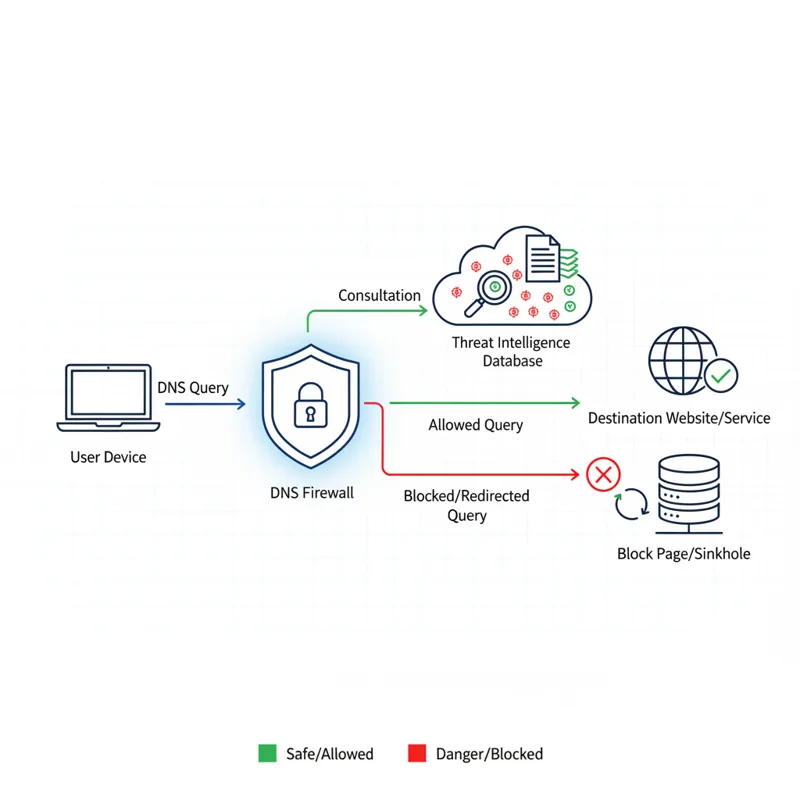
A DNS Firewall operates by intercepting your network’s DNS queries before they reach their intended destination. It acts as a specialized, intelligent gatekeeper for all DNS traffic leaving your network. Unlike a traditional network firewall that primarily inspects IP packets and port numbers, a DNS Firewall focuses specifically on the domain names being requested. Here’s the mechanistic breakdown:
- Query Interception: When a device on your network (laptop, server, IoT device) attempts to resolve a domain name, that query is first routed to your configured DNS Firewall.
- Threat Intelligence Consultation: The DNS Firewall then compares the requested domain against an continuously updated database of known malicious domains. This database, often powered by advanced threat intelligence feeds, includes domains associated with:
- Malware command-and-control (C2) servers.
- Phishing sites.
- Ransomware infrastructure.
- Botnet domains.
- Domains used for data exfiltration.
- Policy Enforcement: Beyond threat intelligence, the DNS Firewall also enforces your organization’s or your personal content filtering and security policies. You can configure it to block categories of websites (e.g., adult content, gambling, social media during work hours) or specific domains.
- Actionable Outcome:
- If Safe: If the domain is legitimate and doesn’t violate any policies, the DNS Firewall forwards the query to a recursive DNS resolver, gets the IP address, and returns it to the requesting device. The user experience is seamless.
- If Malicious/Blocked: If the domain is identified as malicious or falls under a blocked category, the DNS Firewall prevents the resolution. Instead of returning a legitimate IP address, it might return a non-routable IP, an error message, or redirect the user to a safe, custom block page.
Crucially, this blocking happens at the DNS layer, before your device ever attempts to establish a direct connection to the potentially harmful server. This pre-emptive blocking is a significant advantage in threat prevention.
Why DNS is the Ultimate Defense Point Against Modern Cyber Threats

The strategic position of DNS in network communications makes a DNS Firewall an exceptionally powerful security tool, particularly in 2026, where threats are more sophisticated than ever.
Pre-Emptive Blocking of Malware and C2 Communications
Most malware, once it infects a system, attempts to “call home” to a command-and-control (C2) server to receive instructions, download additional payloads, or exfiltrate data. These call-home attempts always start with a DNS query to resolve the C2 server’s domain name. A DNS Firewall can identify and block these queries instantly. If the malware can’t resolve its C2 server’s address, it often becomes inert or significantly less effective, preventing further damage and containing the threat. This is a critical line of defense against sophisticated threats that might bypass endpoint antivirus.
Stopping Phishing and Ransomware at the Source
Phishing remains one of the most prevalent and effective attack vectors. Users, even with training, can accidentally click on malicious links in emails or messages. If that link points to a known phishing domain, a DNS Firewall can prevent the browser from even loading the fraudulent page. Similarly, many ransomware strains communicate with external servers for key exchange or payment instructions. By blocking these DNS requests, a DNS Firewall can sever the ransomware’s ability to fully execute its attack or exfiltrate data, buying precious time for incident response.
Preventing Data Exfiltration and DNS Tunneling
Attackers often use DNS itself as a covert channel to exfiltrate small amounts of data or establish C2 communications, a technique known as DNS tunneling. This involves encoding data within legitimate-looking DNS queries or responses. Advanced DNS Firewalls are designed to detect these anomalies and patterns, blocking the communication and preventing sensitive information from leaving your network unnoticed.
Enforcing Granular Network Policies
Beyond threat blocking, a DNS Firewall provides a powerful mechanism for content filtering and acceptable use policy enforcement. Businesses can block access to unproductive websites, ensure compliance with regulatory requirements, and prevent access to inappropriate content. Individuals can use it to protect children from unsuitable websites or simply improve focus. This granular control over internet access adds another layer of security and productivity.
Enhancing Visibility and Incident Response
A well-implemented DNS Firewall logs all DNS queries and their outcomes. This provides invaluable telemetry for security teams. You gain insight into what domains devices on your network are trying to reach, which can reveal hidden infections, suspicious activity, or policy violations. This data is crucial for faster threat detection, incident investigation, and proactively strengthening your security posture.
Deployment Models: Cloud, On-Premise, and Hybrid
Choosing a DNS Firewall isn’t a one-size-fits-all decision. The deployment model often depends on your organization’s size, infrastructure, and specific needs:
- Cloud-Based DNS Firewall Services: These are increasingly popular, especially for distributed workforces and smaller businesses. Your DNS queries are simply directed to the provider’s global network of resolvers. The filtering and threat intelligence happen in the cloud, often providing rapid updates and scalability without requiring on-premise hardware. This model generally offers a centralized management portal, making administration straightforward.
- On-Premise DNS Firewall Appliances: For larger enterprises with complex networks, strict data sovereignty requirements, or specific integration needs, a physical or virtual appliance deployed within your own network might be preferred. This offers maximum control and potentially lower latency for internal queries but requires more management overhead.
- Hybrid Solutions: Many organizations opt for a blend, using cloud services for remote workers and branch offices, while maintaining on-premise solutions for core data centers. This balances flexibility with control.
What Most People Get Wrong About DNS Firewalls
Even seasoned IT professionals can sometimes misunderstand the specific role and limitations of a DNS Firewall. Here are a few common misconceptions:
- It’s a complete cybersecurity solution: A DNS Firewall is powerful, but it’s part of a layered security strategy, not a standalone defense. It complements, but doesn’t replace, traditional firewalls, endpoint protection, intrusion detection systems, or email security gateways. It protects at the DNS layer, not by inspecting the content of web traffic (HTTP/S payload).
- Any DNS resolver offers the same protection: While some public DNS resolvers (like Cloudflare’s 1.1.1.1 or Google’s 8.8.8.8) offer basic malicious domain blocking, they don’t provide the granular policy control, custom block/allow lists, detailed logging, or enterprise-grade threat intelligence feeds that a dedicated DNS Firewall solution offers.
- It only blocks obvious threats: A sophisticated DNS Firewall integrates with real-time threat intelligence that can detect newly emerging threats, zero-day attacks leveraging new domains, and even domain generation algorithms (DGAs) used by advanced malware. It’s far more dynamic than a static blocklist.
- It’s only for large businesses: The rise of cloud-based DNS Firewall services has made this technology accessible and affordable for individuals and small to medium-sized businesses (SMBs), providing enterprise-grade protection without the enterprise-level complexity or cost.
Implementing a DNS Firewall: Practical Considerations
Adopting a DNS Firewall isn’t overly complex, but a thoughtful approach ensures optimal protection and minimal disruption.
- Assess Your Needs: What are your primary security concerns? Do you need content filtering, robust malware protection, or advanced analytics? How many users do you need to protect, and where are they located (on-site, remote, hybrid)?
- Research Solutions: Evaluate providers based on their threat intelligence capabilities, ease of deployment, management interface, reporting features, integration with your existing security stack, and pricing models. Look for solutions that prioritize user comfort and well-being, similar to how you’d research for a best mattress for side sleepers – focusing on fundamental needs and lasting impact.
- Pilot Program: Before full deployment, run a pilot with a small group of users or a specific department. This helps identify potential issues, fine-tune policies, and demonstrate the solution’s value.
- Configure Policies: This is where you define what gets blocked and what’s allowed. Start with default threat protection policies and then customize content filtering rules based on your organization’s acceptable use policy. Remember to set up custom block and allow lists for specific needs.
- Monitor and Adjust: A DNS Firewall isn’t a “set it and forget it” tool. Regularly review logs and reports to identify trends, fine-tune policies, and respond to any legitimate blocked sites (false positives) or missed threats (false negatives). Threat landscapes evolve, so your policies should too.
- Educate Users: While a DNS Firewall provides excellent protection, user education about phishing, safe browsing habits, and reporting suspicious activity remains crucial.
The Future of DNS Security in 2026 and Beyond
As we look further into 2026 and beyond, DNS Firewalls will continue to evolve. We’re already seeing:
- AI and Machine Learning Integration: These technologies are making threat intelligence even more predictive, capable of identifying malicious domains based on behavioral patterns rather than just static lists. This helps detect new threats faster.
- Protection for Encrypted DNS (DoH/DoT): The increasing adoption of DNS over HTTPS (DoH) and DNS over TLS (DoT) encrypts DNS queries, which is great for privacy but complicates traditional DNS filtering. Leading DNS Firewall solutions are adapting to inspect and enforce policies even with encrypted DNS traffic, often by acting as a trusted proxy or integrating with endpoint agents.
- Closer Alignment with Zero Trust: DNS Firewalls fit naturally into a Zero Trust security model, where no device or user is inherently trusted. By continuously verifying every DNS request, they help ensure that only legitimate and authorized connections are ever attempted, reducing the attack surface significantly.
Frequently Asked Questions About DNS Firewalls
Q: Can a DNS Firewall block all cyber threats?
A: No, no single security solution can block all cyber threats. A DNS Firewall is an extremely effective layer of defense, particularly against malware C2, phishing, and content-based threats. However, it needs to be part of a comprehensive security strategy that includes endpoint protection, email security, traditional firewalls, and user training. It doesn’t inspect the content of encrypted web traffic or prevent attacks that don’t involve a DNS lookup (e.g., direct IP-based attacks, some insider threats).
Q: Is a DNS Firewall difficult to set up?
A: For cloud-based services, setup is often quite straightforward, requiring a simple change to your network’s DNS settings (pointing to the DNS Firewall provider’s resolvers). For on-premise appliances, it can be more involved, but modern solutions are designed with ease of deployment and management in mind. Many providers offer excellent documentation and support.
Q: Does a DNS Firewall slow down my internet?
A: Typically, no. Modern DNS Firewall services are built with high-performance global networks. The latency added by a DNS lookup is usually minimal, often in milliseconds, and the benefits of enhanced security far outweigh any imperceptible delay. In some cases, using a faster, optimized DNS resolver could even improve perceived browsing speed compared to a slow ISP default.
Q: Can I use a DNS Firewall on my home network?
A: Absolutely! Many cloud-based DNS Firewall providers offer free or affordable plans suitable for home users. You can usually configure your home router to use the DNS Firewall’s resolvers, protecting all devices on your network. This is an excellent way for individuals to boost their personal cybersecurity posture against common threats.
Q: What’s the difference between a DNS Firewall and a regular network firewall?
A: A regular network firewall operates at lower levels of the network stack, primarily inspecting IP addresses and ports to allow or block traffic. A DNS Firewall operates specifically at the DNS layer, inspecting domain name requests. It blocks connections before they are even initiated based on the requested domain name, whereas a traditional firewall typically inspects the established connection. They are complementary security tools.
The Ultimate Defense is a Layered Defense
The digital world of 2026 demands proactive and intelligent security measures. A DNS Firewall isn’t just another piece of security tech; it’s a foundational layer that operates where nearly all internet communication begins. By intercepting, inspecting, and intelligently blocking malicious DNS requests, it prevents a vast array of cyber threats from ever reaching their target. Integrating a DNS Firewall into your security strategy, whether you’re a large enterprise or an individual looking to secure your home network, represents one of the most effective and often underestimated steps you can take to build a truly robust defense against the evolving landscape of cyber threats.